Quantum computers — computers that move and store information based on the principles of quantum mechanics — promise super-high-speed computing. But what about super-security? Two U of T Engineering researchers are working to make quantum security protocols accessible and inexpensive, so when the quantum era dawns, your personal data will stay safe.
Professors Hoi-Kwong Lo and Joyce Poon (both ECE) are working on quantum key distribution, a method of sharing a secret key to encrypt and decrypt information with security guaranteed by quantum mechanics. In situations that require impenetrable communication systems for exchange of information, this method of encryption is used — but it comes with a cost, and a footprint.
Despite its effectiveness, use of quantum key distribution is limited because it requires large and complicated equipment. “Right now it is only used in very select industries, like some military and financial institutions,” says Lo. “It’s a niche market because it’s so expensive, and the equipment involved uses discrete components.” Classical methods of producing encryption keys that allow you to shop online with relative security are generated from computational methods. Currently, such classically encrypted keys are secure, but should quantum computers emerge in the near future this type of encryption could be breached. Lo and Poon are working on a way to make quantum key distribution low-cost and accessible for consumer use.
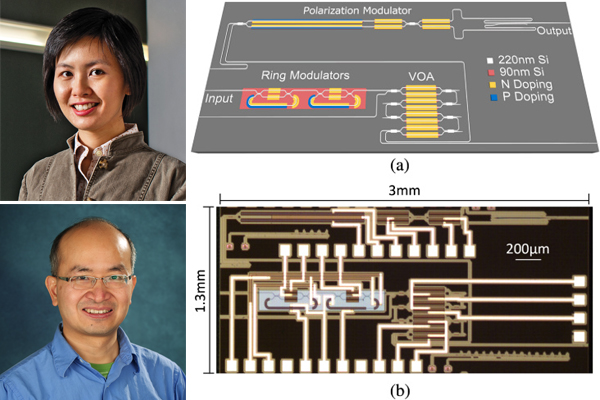
In a paper recently published in Optica, the research groups of Lo and Poon demonstrate an optical transmitter chip for quantum key distribution using a generic silicon photonic process — showing the potential of using wafer-scale fabrication to minimize and reduce the cost of optical components for quantum key distribution encryption methods.
“Classically, we do not send one photon at a time, so someone who wiretaps can just tap off a little bit of those transmitted photons and you would not really have noticed the disruption,” says Poon. “Imagine sending one photon in a random polarization at a time: if someone steals or intercepts a photon in the middle, it would be possible to detect the breach because of the quantum no-cloning theorem.” The challenge is to develop integrated and miniaturized devices for creating these breach-proof encryption keys.
Their solution is to use the existing and well developed infrastructure of semiconductor electronics manufacturing to create silicon photonic integrated circuits for quantum key distribution. Leveraging the existing infrastructure to make the photonic components not only reduces the costs but enables the integration of many devices on the same chip within a millimetre of each other. This is the first time a quantum key distribution transmitter has been integrated on a standard silicon photonic chip.
This new method of achieving quantum key distribution could mean the encryption measures used in sectors with high security requirements could one day be used to protect your personal information like health records and credit card statements. “It’s a practical but elegant approach,” says Poon. “It’s exciting because it really brings together the possibility of integrating quantum communications and classical communications in a very small package.”